|
| "We have discovered a process of great practical value in authentication which has been overlooked by thousands of workers who have spent years in the field, especially those working on FIDO Alliance technologies."
|
| All those who are committed to existing multi-factor authentication systems, including passkeys, are like
engineers in the 1890s working diligently to perfect the telegraph system; all their work will soon be eclipsed by a much better technology.
|
| Current MFA systems are NOT secure: FBI Issues Surprise New Cyber Attack Warning:
Multi-Factor Authentication Is Being Defeated. WebAuthn+ is secure against the attack scenarios described in that article.
|
 |
| Cryptography Fundamentals
|
| While the mathematics of implementing a cryptographic system can be very complex, the basic principles are quite simple.
|
| There are two broad categories of encryption: Symmetric
and Asymmetric. Symmetric encryption depends on a single key that needs to be shared
among the people who encrypt and decrypt messages. Symmetric encryption can be very secure if the key is strong
and protected. The bureaucratic nightmare of securing and administering secret keys inspired the creation of Asymmetric encryption
which is usually referred to as Public-Key Cryptography.
|
Here is everything you need to know about the magic of Public-Key Cryptography: There are two keys,
a public key which everyone has access to and a private key which you must keep private for
the system to be secure. If a bad actor gets access to your private key it is game over; you lost.
- A message that is encrypted with your public key can only be decrypted with your private key.
If you keep your private key private, anyone can send you a secure message by accessing your public key.
- When you send a message and sign it with your private key, your signature can be confirmed with your public key.
If you keep your private key private, the validity of your signature is assured.
|
| That is the essence of Public-Key Cryptography.
|
 |
| In the WebAuthn+ process the credential provider sends messages
from the application server to your smart phone through an encrypted Firebase channel.
A message can only be decrypted with your private key which is stored securely on your smart phone.
|
| What do you mean, "stored securely on your smart phone"? Is that a joke? We all
know from the Apple v FBI encounter
that anything on your smart phone can be decrypted by anyone with marginal computer skills. It is incredibly easy to do.
|
| Well... it is not easy to do if the encryption process is done in a sensible manner
(send the following architectural overview to your friends at Apple).
|
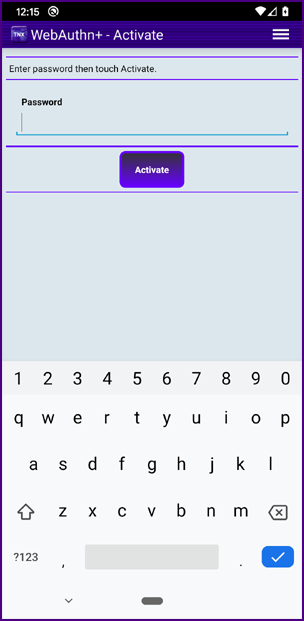
| When a user downloads and activates the TNX WebAuthn+ mobile app from the Apple App Store or from the Google Play Store,
in the installation process the mobile app generates a 4,096 bit public/private key pair in less than ten seconds (on a "good" phone). A 4,096 bit key pair is very large and highly secure
(double the traditional recommendation by RSA Laboratories [ref]).
|
| The public key is uploaded to the mobile app provider's (e.g., your bank's) data structures.
The private key never leaves your smart phone. The private key is stored on your smart phone in an encrypted state.
|
 |
|
In order to attain a high level of security an AES-256
symmetric key is also created when the TNX WebAuthn+ mobile app is installed. This AES-256 key is used to encrypt/decrypt data on the smart phone;
this key is not stored on the smart phone.
|
|
When the TNX WebAuthn+ mobile app is installed the user creates a password for the app. This password is used to create an
obfuscated identifier (details below) which is associated with user's AES-256 key and stored in the mobile app provider's data structures. When a user initializes the TNX WebAuthn+ mobile app the password is entered and the obfuscated identifier is re-created and sent to the server, the AES-256 key is returned.
|
|
When a user enters his/her password in the TNX WebAuthn+ mobile app, after a configurable number of failed attempts (bad password entries) the mobile app locks and
the assistance of a personal banker (or a team member from corporate security, etc.)
is required to reconfigure the app. Don't forget your password unless you want to see your personal banker or a team member from corporate security, etc.
|
|
Because after a configurable number of failed attempts (bad password entries) the mobile app locks, it is impossible to attack
WebAuthn+ through a brute-force attack (there is no way for a bad actor to get the AES-256 key).
|
| It is important not to associate the user's AES-256 key with the user in the server data structures.
Associating the user's AES-256 key with an obfuscated identifier
and not the user's account limit's the possibility that a bad actor within the mobile app provider's organization could gain access to a user's symmetric key,
steal the user's smart phone and gain access to the user's accounts.
|
|
The only way to secure data on a smart phone is to encrypt the data with a key that is stored off the device,
delete the key from the smart phone when it is not needed and load the key in a secure process when it is needed.
Our process takes just a few seconds and is within the boundaries of being user friendly.
|
| So if your smart phone is lost or stolen, a bad actor cannot sign on to
your TNX WebAuthn+ mobile app; and if a bad actor can programatically gain root access to your smart phone
and read the stored data, the important data (i.e., your private key) is securely encrypted.
|
| If a government agency ordered a service provider to decrypt the data on a user's smart phone, the service provider would not be able to comply if the user has chosen a complex password for the TNX WebAuthn+ mobile app (technical details below)
|
| Wait a minute!!! The weak link of the system depends on a user's password??? That can't be good.
|
| There is a significant difference between a web application which is a distributed application running on multiple systems (and in multiple browser applications) and a mobile app running on a single system that you control. The only way a password that you enter into the TNX WebAuthn+ mobile app can be intercepted is if there is malware running on your phone (game over, you lost) or if a bad actor "looks over your shoulder", steals your password, then steals your smart phone, and defeats the fingerprint reader (or other security) before you can report your smart phone lost or stolen... then the bad actor can access your account; this is the only real threat vector against TNX WebAuthn+.
|
| Why don't we just use the security key within the
Trusted Platform Module provide by the phone manufactures?
There are both social reasons and technical reasons. Big corporations have now proven that they cannot be trusted with our personal data AND they cannot be trusted
not to collude with evil governments.
There are also numerous technical reasons not to trust TPM:
click here for details
|
 |
| Here are the details: |
| In order to protect the private key and other data within the TNX WebAuthn+ mobile app,
access to the app is protected by a password and that password is used to generate an obfuscated identifier that is associated with the user but cannot be used to identify the user, for example:
|
| 2E988595485874A71449546BB49A7AFC9B603ED5EFFD7A5DAC9B8B333A345B78
|
| The obfuscated identifier is created using the
PBKDF2WithHmacSHA256 secret key algorithm. The two most important inputs into this algorithm are the password itself and the iteration count.
The more complex the password and the higher the iteration count the higher the computational cost for anyone trying to crack the secret key.
|
|
The PBKDF2WithHmacSHA256 secret key is also used to encrypt/decrypt the AES-256 key which is then stored on the server in an encrypted state.
|
|
When a user enters his/her password in the TNX WebAuthn+ mobile app this obfuscated identifier is generated and sent to the server. The AES-256 key is returned.
|
|
| The reference implementation uses an iteration count of 262,144.
The iteration penalty is imposed every time a user enters his/her password and activates the TNX WebAuthn+ mobile app.
On a good phone the time penalty is about 2.5 seconds (about the limit for a "bad" user experience).
|
| If a government agency ordered a service provider to decrypt the data on a user's smart phone, and the service provider had access to the smart phone,
in theory, a brute force attack could be made by testing all the obfuscated identifiers in the service provider's system. If the user chooses a password that is ridiculously easy to guess (e.g., "password", "123", "asdf") then the quality of the algorithm and the iteration count do not make a difference. The system is vulnerable.
|
| On most mobile app keyboards there are 82 characters to choose from
(26 lower case, 26 uppercase, 10 numeric and 20 symbols). If a user creates a password with twelve characters there are 82 to the 12th power possible permutations
to consider when cracking the secret key generated from the password:
|
| 82^12 = 92,420,056,270,299,898,187,776
|
| That is 92 sextillion and change. If you randomly go through half the possibilities, you have a about a 64% chance of hitting the right password.
How long would that take if each guess took 1 second to compute on a very fast computer and you had an array of one million computers?
|
92,420,056,270,299,898,187,776 / 2 (half the possibilities for a 64% probability) /1 million computers
/ 60 seconds in a minute / 60 minutes in an hour / 24 hours in a day / 365 days in a year = 1,465,310,380 years
|
| That's 1.465 billion years; the age of the Earth is estimated at 4.543 billion years. In cryptography the key is to use algorithms
that require a significant time penalty to defeat.
|
| Assume that a user chooses an eight character password. The number of possibilities is 82^8 = 2,044,140,858,654,976
and the time calculation goes to 32.4 years; not great but maybe "good enough".
|
| Assume that you are trying to protect some system like your phone with a four digit PIN.
Well, that is only 10,000 possible combinations and the system could be cracked in a matter of seconds. Assuming that the iPhone was protected by a PIN or a weak password,
it really was no big deal that the FBI was able to crack the system.
|
| A technical overview of WebAuthn+ can be found here:
WebAuthn+ ~ Unhackable Authentication
|
 |
| Cryptographically Secure Digital Credentials
|
|
In the late Seventies and early Eighties computer names were maintained
by using handcrafted HOSTS.TXT files. As networks became more interconnected this process became unmanageable.
Everyone knew that something needed to be done. When the
Domain Name System (DNS)
was created everyone saw it as the obvious solution.
|
|
Similarly, when the solution to cybersecurity authentication emerges,
everyone will say, "Of course, this is how it had to be."
|
|
Whenever a significant technology problem is solved, incredible new opportunities arise.
Solving the Domain Name System (DNS) problem made the creation of the information Internet possible.
Solving the authentication problem will make the Internet of Value possible.
|
| The Internet of Value
has the potential to ignite a worldwide renaissance by providing, "ubiquitous access to efficient financial systems
and the ability to transact with anyone in the world."
~ W3C - Internet of Value Manifesto ~
|
| The basic question is, how can trust be established in the digital age?
If you and I have never met and I come to your website or place of business, how can you
be confident that my digital credential is valid?
The Trust Nexus answers this basic question regarding the
establishment of trust.
|
| The essence of our system is incredibly simple:
Through cryptographically secure digital credentials,
we do away with the weaknesses of user names and passwords for web authentication.
If a credential is provisioned to a
user's smart phone in a valid institutional process, then when the user presents the
credential (either in person or over the network) the receiver can be highly certain that the
credential and the user are valid.
|
| There is only one threat vector:
If a bad actor "looks over your shoulder", steals your password, then steals your smart phone, and defeats the fingerprint reader (or other security) before
you can report your smart phone lost or stolen... then the bad actor can access your account.
|
| Because the receiver can cryptographically verify that you are the person to whom
the credential was issued, under the Trust Nexus
it truly does not matter who you are;
what matters are institutional validations
and the ability to represent those validations with cryptographically secure digital credentials.
|
| What is a valid institutional process?
|
|
It is the identity proofing process. It can be anything the institution defines and controls, from the very simple to the highly secure. In the most basic use case,
the credential provider of a web application simply wants to secure the account to the user who created the account. Identity attributes
do not need to be verified; valid authentication (from the user who created the account) simply needs to be secure and repeatable.
Under this use case a credential can be issued directly through a web application when the account is created; the identity proofing could be an email verification.
|
|
The process for creating a Cryptographically Secure Digital Credential can also be
applied in a secure setting where identity is verified
(e.g., the issuance of corporate identity credentials at a security station or the issuance of financial
credentials at a bank, "know your customer"). This secure "identity proofing" represents a high level
institutional validation and can be a very complex process. This process will eventually be simplified using a
Digital DNA ID or Iris ID (see below).
|
|
Under the Trust Nexus
the user's identity is verified in a valid institutional process determined by the institution issuing the credential.
There is no master identity proofing process that one organization or a government controls.
The identity proofing takes place by the institution when a digital credential is issued.
|
 |
| Under the Trust Nexus
the concept of identity is fundamentally changed. Who are you?
You are the entity that has been issued a cryptographically secure digital credential.
|
The traditional view of identity is that you are a collection of
identity attributes (e.g., user name, first name, last name, address, account number, credit history, etc.) and you then
prove your association to these attributes through one or more of the
three factors of authentication:
- Something you know (password, secret question)
- Something you have (security token, USB key, mobile device)
- Something you are (biometrics)
|
| Rather than proving an association to a set of attributes, the foundation of WebAuthn+
is the process of using cryptographically secure digital credentials in valid institutional processes. The concept of verifying institutional validations
rather than verifying personal data requires a shift in perspective. Once that mental shift occurs
everyone is amazed at how simple our system is.
|
| Think of your smart phone as a security device for securing your private key and your association to your digital credentials.
|
Access to your phone can be thought of in terms of the three factors of authentication:
- Something you know (password)
- Something you have (the phone itself)
- Something you are (fingerprint scanner)
|
| However, once you have established a legitimate association to your private key, the digital credential process takes over.
We have essentially created a single sign on process with the user's smart phone as the point of entry to the digital credentials that provide more granular application access.
|
| Signing on to a mobile device that you physically control is qualitatively different than signing on to a web based application from any system in the world. Your digital credential is cryptographically locked to your mobile device; it cannot be "spoofed" or replicated. Along with the cryptographic processes, the "something you have factor" (the physical smart phone itself) provides enhanced security.
|
| Again, there is only one threat vector
against WebAuthn+:
If a bad actor "looks over your shoulder", steals your password, then steals your smart phone, and defeats the fingerprint reader (or other security) before
you can report your smart phone lost or stolen... then the bad actor can access your account.
|
| If a bad actoor, like Jack Bauer, were to kidnap you and torutre you for your application password, your could enter a fake password that would act as a
duress code and alert the authorities of your location.
|
 |
| Think of Identity and Authentication Management in terms of referencing institutional validations represented by
cryptographically secure digital credentials,
not in terms of managing and verifying certificate chains of authority, or even worse, managing and validating vast amounts of personal or biometric data.
|
| Your identity is not determined by a collection of attributes; your identity is determined by a cryptographically secure digital credential
that associates "you" to a public key. For each specific context, the essence of "you" is determined by an institutional validation.
|
| If your bank validates you and issues you a digital credential, your identity does not matter, all that matters is that you are the only person who can utilize that credential.
Think of the past when the king's seal represented a stamp of approval; your identity did not matter, all that mattered was the validity of the king's seal
and that you were the rightful holder of the credential. In the age of technology it is possible to create a
"valid seal" with a secure private key
on a smart phone.
|
| A cryptographically secure digital credential is an inviolable proxy to the
valid institutional process that was used for identity proofing. Once the institution determines that "you are you", the digital credential
can be used to verify that institutional validation.
|
| It will be simple to make cryptographically secure digital credentials
interoperable amongst various institutions (e.g., a group of universities) and/or commercial enterprises.
Federation will be just a matter of sharing user identifiers (usually an email address) and the associated public keys (along with a valid process for a credential revocation check).
|
| Surprisingly, there is no need to store user credentials or identity data in any type of worldwide data structure.
All that is necessary is to have sufficient information to validate the credential provider (bank, insurance company, government passport agency, etc.) because their private key is used to sign a hash of all the credentials they issue.
|
| All that is needed to validate the credential providers is a trusted reference:
The Worldwide Distributed Ledger of Credential Providers.
|
 |
|
Establishing Security and Good Will
|
|
A system is secure if the plans for the system are public, and the bad actors can still not break in.
|
|
Our source code is available for
download.
|
|
An organization can maintain complete control
of its authentication process under the Trust Nexus. When there is no need for third party validation of credentials
(e.g., a corporation or government agency simply wants to authenticate its own users or a service like Netflix just wants to authenticate its own members) our infrastructure technology can exist as an
insulated microcosm within corporations or
government agencies.
|
|
When third parties must rely on credentials
(e.g., drivers licenses, passports, financial credentials, insurance credentials, etc.) there will be
a public identity infrastructure that will be managed through
The Worldwide Distributed Ledger of Credential Providers.
|
 |
|
Not PKI
|
|
While many of our cryptographic processes are similar to the processes used in
Public Key Infrastructure (PKI),
we avoid the bureaucratic inconveniences and lax security inherent in PKI.
[ref]
Under PKI, when a digital certificate is issued, the user (or a malicious administrator or someone who can access the user's system)
can simply "share" the cert with anyone. Under the
Trust Nexus it is far less likely that a user will share his/her
smart phone and password.
|
|
Also, under the Trust Nexus a catastrophic security
breach of the PKI, similar to the
Comodo Security Breach,
would have no ill effects for users. Contrary to the proponents of PKI, a Comodo-like security breach is
always a possibility, especially if you travel to a hostile foreign country or if you are a citizen under an
oppressive regime.
|
|
The most significant advantage the Trust Nexus
has over traditional PKI is that there is no certificate chain of authority to maintain and no cumbersome bureaucratic processes.
|
|
Removing the need for a Trust Authority to verify billions
of individual identities and manage billions of public/private keys makes a world wide system practical.
|
 |
|
Protecting Privacy
|
|
One of the most important aspects of our technology is that
we secure identity while protecting privacy. Our technology provides a
100% privacy protection. We do not store any personal data,
When there is a need for third party validation we simply register the public keys of credential providers.
We change the mind set of authenticating using personal data; instead, the only thing that matters is an
institutional validation represented by a
cryptographically secure digital credential.
|
|
If you are a member of the Secret Moose Lodge of Ottumwa, Iowa,
your digital credential can be validated under the Trust Nexus without
any detailed information about you or your organization being revealed.
|
 |
|
Aren't biometric factors supposed to "save the day"?
|
|
There are severe limitations in using biometric data over a network or
in a physical location with no monitoring; one of the most notable failures of biometrics
is the "Gummi Bear Hack" used by Australian
school children to defeat fingerprint sensors (verified by Japanese researchers)
[refA]
[refB].
|
|
A group of German hackers cracked the iPhone fingerprint scanner
just two days after Apple Inc. launched the technology that it promises will better protect devices from
criminals and snoopers seeking access
[ref].
|
|
A
technical update from Ars Technica
detailed the continued problems with fingerprint authentication.
|
Even with all their intellectual brain power, Microsoft is having problems implementing biometrics:
Hackers Got Past Windows Hello by Tricking a Webcam
|
|
Phone manufactures are touting biometric integration (most notably enhanced fingerprint scanners).
They are overlooking a disastrous use case: What happens if a paramour drugs you and uses your finger to unlock your phone and financial accounts?
Or even worse, Jack Bauer cuts out your eyeball and uses it to"fool" an iris scanner.
|
|
Even the fingerprint readers on smart phones can now be hacked:
Biometric auth bypassed using fingerprint photo, printer, and glue.
|
|
A biometric identifier is like a "magic word"
that supposedly only the person associated with the identifier can say. But once the
"magic word" is spoken anyone who can
access the identifying device (or the resulting digital stream) can speak the
"magic word" and steal the user's identity, especially when authenticating over a network or in a physical location with no monitoring.
|
|
Governments that attempt to create vast repositories of biometric information will simply
be storing extremely long "magic words" that are available for compromise at a single point of failure.
|
|
The "dirty secret" of biometrics is that biometrics are very poor for establishing an Internet identity infrastructure;
however, biometrics are great for destroying privacy and establishing a "Surveillance Society" because the biometric identification process is "good enough"
to track large numbers of individuals.[ref]
|
|
One of the most problematic biometric identifiers is facial recognition.
The potential for abuse and errors recently caused IBM, Amazon and others to abandon facial
recognition.[refA] [refB]
|
|
With continuous improvements the accuracy of facial recognition is becoming impressive. These improvements will continue and in a very short time facial recognition will be considered reliable and effective. The social problems associated with facial recognition are social problems, they are not technology problems. An enlightened society will create solutions for these social problems.
|
|
"Broadly, facial recognition systems can be used to accomplish one of two different tasks: verification or identification. Verification (also known as 1:1 matching) is used to confirm that a person is who they say they are. An example of verification is when a person uses their face to unlock their smartphone, sign into a banking app, or verify their identity when boarding a plane. A sample image is taken of a person's face during login, which is then compared to a known image of the person they claim to be. Facial recognition algorithms tend to have good accuracy on verification tasks, because the subject usually knows they are being scanned and can position themselves to give their cameras a clear view of their face."[ref]
|
|
"Identification (also known as 1:N or 1:many matching) is when software takes an unknown face and compares it to a large database of known faces to determine the unknown person's identity. Identification can be used on 'cooperative' subjects who know they are being scanned, or 'uncooperative' ones who do not. The latter has drawn the most attention, due to the fear that law enforcement or private businesses will use the technology to remotely gather data about individuals without their knowledge. However, remote identification can also be used to identify suspects from surveillance footage, track down missing persons or the victims of kidnapping, and improve private sector services. Remote identification systems tend to have lower accuracies compared to verification systems, because it is harder for fixed cameras to take consistent, high-quality images of individuals moving freely through public spaces."[ref]
|
|
When the person is present and the biometric data can be verified in the presence of a security agent or in a public place that diminishes the possibility of hacking (e.g., an airport kiosk, a retail check out, a police state check point or surveillance video), the utility of biometric processes increases significantly; in fact, this is the only valid use case for biometric factors. Over a network or in a physical location with no monitoring, biometric
identifiers can NEVER be trusted.
|
|
It is possible to protect privacy and limit surveillance when creating a system that utilizes biometrics. The key is to give the user control of their biometric data and restrict the use of that data by corporations and governments.
|
|
When used purely for identification (1:1 matching) the biometric data
could be embedded within a cryptographically secure digital credential at the time the credential is issued. A hash code of the biometric data would be signed with the private key of the credential issuer. In real time verification the individual's biometric factor could be compared with biometric data in his/her credential. If there is a match, it can be concluded that the individual presenting the credential was the individual to whom the credential was issued.
|
|
Through a Bluetooth Low Energy (BLE) connection it will be possible for a digital credential issued to your smart phone to interact with a retail check out system or airport security kiosk that verifies your facial biometric. There would be no check against an Orwellian repository of biometric information; the user would carry his/her own biometric data and be in complete control of its use.
|
|
A user could authorize the organization that issues their digital credential (e.g., bank, financial institution, insurance, travel security) to hold a copy of their biometric data to be used exclusively for credential restoration. If you were traveling in a foreign country and lost your smart phone you could purchase a new phone, go to a local bank and have the credential for your bank restored to your smart phone.
|
 |
|
Legal Identity ~ Digital DNA and IRIS ID
|
|
Even with increasing accuracy, facial recognition and other prevalent forms of biometric identification are
NOT 100% accurate.
|
|
When you establish an account with Netflix or some other service organization there is no need to provide your absolute legal identity;
all that is needed is an application identity.
You just need some way to secure your account; a digital credential that only you can use works fine in this use case. In fact, WebAuthn+ works flawlessly in this scenario. If your smart phone is lost or stolen
you can buy a new smart phone and reestablish your digital credential through a trusted email account. Not perfect, but probably good enough.
|
|
For banking credentials, insurance credentials, state issued credentials (e.g., driver's licenses, passports) you need a process
that securely establishes your legal identity. Currently there is a "hodgepodge" of processes. Every financial institution and government agency has their own process for identity proofing (i.e., institutional validation). All of these processes, especially current biometric processes based on facial recognition or other biometrics, are flawed.
|
|
What if there was a foolproof biometric identifier that established identity with absolute certainty? There are two:
Digital DNA ID and Iris ID. There are no other biometric identifiers that are more accurate.
|
|
Iris ID is available now and may be the most pragmatic biometric choice.
|
|
In the near future, when a financial institution or state agency first provisions a digital credential they will take a DNA sample that will be digitized in a manner of minutes.
This Digital DNA ID will be the secure identifier for your account. Once your digital credential is provisioned to your mobile device, the security of the WebAuthn+ process takes over.
If your digital credentials are ever lost or stolen you can reestablish your
digital credentials simply by being you.
|
|
Credential restoration is one of the primary attack vectors against an identity system. If a bad actor can convince an organization that credentials have been lost or stolen and they can scam the process for credential restoration, they can steal another user's credentials. A completely secure credential restoration process will be the main driving force behind Digital DNA ID.
Customers will feel more secure dealing with a bank where only someone with their Digital DNA ID can access their account.
|
|
Under the Trust Nexus it will be possible to
securely store a Digital DNA ID within a user's credential
when the credential is created by the provisioning institution.
In cases where extreme security is required, verifying the Digital DNA ID in the credential against the individual in real time will provide absolute security.
|
| A Digital DNA ID check in real time mitigates the only
threat vector against WebAuthn+:
If a bad actor "looks over your shoulder", steals your password, then steals your smart phone, and defeats the fingerprint reader (or other security) before
you can report your smart phone lost or stolen... then the bad actor can access your account.
|
|
Government / corporate surveillance and invasion of privacy will become even greater threats in the presence of a technology that establishes absolute identity. The technology itself is not the problem. Government / corporate abuse is the problem. Democratic societies will need to establish laws that prevent this abuse because
the technology is definitely coming.
|
|
One way to limit the potential abuse is to limit the information that can be in a Digital DNA ID. The following excerpt is from the website of ANDE, the makers of a rapid DNA processing system:
|
|
[Begin quote:] Digital DNA IDs are not Genetic Profiles - the two tests look at different aspects of an individual, are performed for different purposes. A Digital DNA ID simply identifies an individual, while a Genetic Profile is designed to assess the health of an individual, and contains essentially every piece of genetic information in the human genome. To put this in perspective, a Digital DNA ID contains approximately one-millionth of the information in a Genetic Profile.
|
|
Digital DNA IDs are the optimal identification tool for two major reasons:
|
- DNA IDs are far more accurate than any other biometric modality including conventional fingerprints, facial recognition, iris scans, and voice recognition.
- DNA IDs preserve privacy - they contain absolutely no useful information about an individual other than identification. A DNA ID contains much less usable information than an individual's address, phone number, photograph, or browser search history.
|
|
The ability of DNA IDs to identify a person with exquisite accuracy is accompanied by an emphasis on privacy protection - the DNA ID generates absolutely no information concerning an individual's health or body composition or organic strengths or weaknesses. [:end quote]
|
 |
|
In the near future, when legal identity is required it will be based on Digital DNA ID.
|
|
When a child is born his/her parents will be issued a digital birth certificate with the child's Digital DNA ID encoded into the digital credential. This digital birth certificate will also include a copy of each of the parent's digital birth certificates. This digital credential will be stored with the hospital where the birth occurred and with the county department responsible for registering births. If the user loses his/her digital credential birth certificate it can be easily recovered with a Digital DNA ID verification (1:1 matching).
|
|
When the child passes his/her driver's license test he/she will be issued a digital driver's license by the state/province department of motor vehicles; the child's Digital DNA ID will be encoded into the digital credential. A verification will be made against the child's digital birth certificate to establish another link in the child's legal identity.
|
|
A similar process will occur when the child receives his/her passport, financial credentials, insurance credentials or any credential that depends on legal identity (e.g., government services).
|
|
With the technology to absolutely verify an individual's legal identity there will be significant opportunities for abuse by corporations and governments in tracking personal data. The technology is coming. There will be no way to hold it back. Again, the social problems associated with biometrics are social problems, they are not technology problems. An enlightened society will create solutions for these social problems.
|
|
Democratic societies that respect human rights will have ample opportunity to witness the abuses of government/corporate
surveillance because in totalitarian states this technology will most certainly run amuck. See China's
Social Credit System.
|
 |
|
Zero Trust Architecture
|
|
Zero Trust Architecture is THE security architecture of the future.
|
|
Within ten years every organization concerned with security will implement Zero Trust. Every major IT vendor will have a Zero Trust offering.
|
|
"The main concept behind zero trust is that devices should not be trusted by default, even if they are connected to a managed corporate network such as the corporate LAN and even if they were previously verified... The once traditional approach of trusting devices within a notional corporate perimeter, or devices connected to it via a VPN, makes less sense in such highly diverse and distributed environments."
|
|
"Instead, the zero trust approach advocates mutual authentication, including checking the identity and integrity of devices without respect to location, and providing access to applications and services based on the confidence of device identity and device health in combination with user authentication."
[ref]
|
|
Solving the authentication problem is the essential first step in implementing a Zero Trust Architecture.
|
|
WebAuthn+ will be a foundation pillar of Zero Trust.
|
 |
|
Will "Self-Sovereign Identity" provide a magical solution?
|
|
"Self-Sovereign Identity" (aka, "Decentralized Identity"), "...is the concept that people and businesses can store their own
identity data on their own devices, and provide it efficiently to those who need to validate it, without relying on a central repository of identity data."
[ref]
|
|
This is exactly what the Trust Nexus does with cryptographically secure digital credentials.
Once a digital credential is issued, all the user's information can be contained securely within the credential and the user has complete control.
There is no need for a central repository of identity data.
Our difference is that we think the credentials themselves, when issued by a legitimate credential provider (bank, passport office, DMV, etc.), will be sufficient.
There is no need to store claims, proofs, and attestation on a blockchain in a distributed database.
The size and complexity of such a system would be ridiculous.
|
|
As long as you can trust the legitimacy of a credential provider, you will be able to trust the claims contained within the digital credential;
the assumption is that the credential provider has put the user through a legitimate identity proofing process.
|
Currently, the missing piece to the puzzle is a simple and elegant process for verifying the legitimacy of credential providers.
The Worldwide Distributed Ledger of Credential Providers (which will contain no user data)
will complete the puzzle.
|
 |
|
Voting From Your Kitchen Table
|
|
WebAuthn+ will greatly influence political events by reintroducing classical Greek democracy to the world. Unlike current on-line polls that can be "spammed" multiple times by a single user or a group of users, on-line polls conducted under WebAuthn+ will be validated for user uniqueness and still be anonymous. Users could also volunteer to provide their demographic profiles to the on-line pollsters enabling political scientists to extricate more meaningful conclusions from their polls.
|
|
At first, this uniqueness will probably be based on a cryptographically secure financial credential.
|
|
Ultimately, with digital driver's licenses and state identity cards based on Digital DNA ID, secure on-line voting will become a reality that will lead to an ever-increasing number of local, national and world plebiscites. There will come a time in the near future when a consortium of major news organizations will call a worldwide referendum.
|
|
Solving the authentication problem will bring the world together and enhance democratic institutions.
|
|
Assume this is coming and ask yourself, "What will be the first issue the entire world will vote on?"
|
 |
|
The Trust Nexus system will integrate biometrics (iris scans and digital DNA) into digital credentials; the system will be simple,
effective, low cost, easy to implement and cryptographically secure.
|
| While the Trust Nexus may "defy conventional wisdom",
we are confident our core ideas are
"non-consensus and right".
|
|
The Trust Nexus will not attempt to compete against the dozens of existing players in the identity management space. We intend to license our authentication technology to all players for a nominal fee; this will insure a rapid and widespread implementation.
|
 |
| For more technical details please see the Cryptographic Overview.
|
 |
|
|